tcpdump on Mikrotik
One of the first source of information for a Linux network administrator is the tcpdump command. If you need it, you already know it, so I’ll not dive into its details. Mikrotik RouterOS on the other hand offers a very similar sniffing tool but without the flexibility of the Linux shell: /tools sniffer. How to have the same flexibility on Mikrotik? Easy: join the best from both worlds by streaming.
While the filtering options of Mikrotik sniffer are enough to focus on the traffic you need, one of the best options is the streaming feature. By streaming all the captured traffic to an external box, you can than use tcpdump or wireshark to further filter the traffic. You just have to inform the router of the destination address all the traffic must be forwarded to.
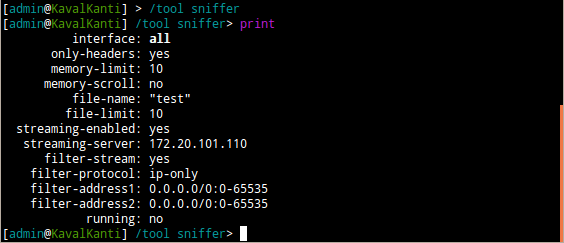
As you can see from the screenshot it’s quite easy: just use /tools sniffer set streaming-server=“your linux box address” streaming-enabled=yes and then do /tools sniffer start. All the traffic captured by RouterOS sniffer will be forwarded to streaming-server address where you can use your favourite tool to inspect it. The forwarding uses TZSP protocol to encapsulate the traffic.
